Deepfakes, powered by AI, represent an evolving and formidable challenge. Capable of generating synthetic media, including videos and audio recordings, with impressive realism, they blur the line between reality and fabrication.
Today, threat actors exploit disinformation campaigns and deploy deepfake content to deceive the public, sway political outcomes, perpetrate fraud, and manipulate stakeholders within corporate environments.
The shift to online interactions amidst the pandemic has amplified these concerns, with many organizations now viewing deepfakes as a more significant risk than identity theft, for which deepfakes can also be employed. This heightened concern is underscored by a recent University College London (UCL) report, which identifies deepfake technology as one of the top threats facing society.
Already, we’ve seen them infiltrate political campaigns, with fake robocalls mimicking candidates’ voices in attempts to deceive the public. These manipulations aren’t just limited to politics; they can spread misinformation, tarnish reputations, and even disrupt financial markets.
Experts estimate that by 2026, 90% of online content may be synthetically generated.
As an employee, being able to discern between authentic content and deepfakes is more critical than ever. Understanding the various forms of deepfake manipulation is paramount for navigating today’s digital landscape and protecting modern businesses.
While deepfakes offer creative possibilities, their potential for misuse is concerning.
Identifying Various Types of Deepfakes in Business Environments
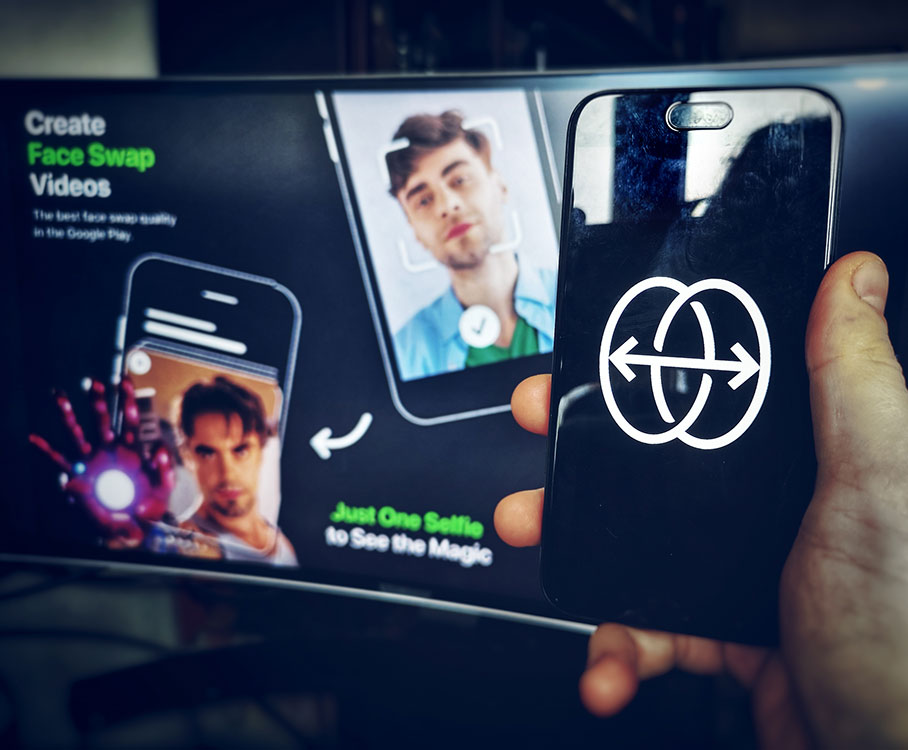
Face-Swapping Deepfakes
In business contexts, face-swapping deepfakes represent a significant threat. These manipulations seamlessly replace one individual’s face with another’s in videos, often with remarkable realism.
To detect them:
- Look for inconsistencies: Pay close attention to lighting, skin tones, and facial expressions. Do they appear natural and consistent throughout the video? Look for subtle glitches such as hair not moving realistically or slight misalignments around the face and neck.
- Check the source: Where did you encounter the video? Was it on a reputable news site or a social media page? Be cautious of unverified sources and unknown channels.
- Listen closely: Does the voice sound natural? Does it match the person’s typical speech patterns? Incongruences in voice tone, pitch, or accent can be giveaways.
Deepfake Audio
Deepfake audio poses a serious risk in the business world. This type of deepfake involves creating fabricated voice recordings. These recordings are generated using advanced artificial intelligence algorithms to mimic the speech patterns, intonations, and nuances of a specific individual’s voice. In business contexts, deepfake audio poses a multifaceted threat. Scammers can exploit this technology to craft deceptive messages, impersonate company executives, or manipulate audio evidence in legal proceedings.
To detect them:
- Focus on the audio quality: Deepfake audio can sound slightly robotic or unnatural. This is especially true when compared to genuine recordings of the same person. Pay attention to unusual pauses as well as inconsistent pronunciation.
- Compare the content: Does the content of the audio message align with what the person would say? Or within the context in which it’s presented? Consider if the content seems out of character or contradicts known facts.
- Seek verification: Is there any independent evidence to support the claims made? If not, approach it with healthy skepticism.
Text-Based Deepfakes
Emerging as a significant concern for businesses, text-based deepfakes mimic the writing style of individuals or publications. Scammers can use these to spread misinformation or impersonate someone online.
To detect them:
- Read critically: Pay attention to the writing style, vocabulary, and tone. Does it match the way the person or publication typically writes? Look for unusual phrasing, grammatical errors, or inconsistencies in tone.
- Check factual accuracy: Verify the information presented in the text against reliable sources. Don’t rely solely on the content itself for confirmation.
- Be wary of emotional triggers: Be cautious of content that evokes strong emotions. Such as fear, anger, or outrage. Scammers may be using these to manipulate your judgment.
Deepfake Videos with Object Manipulation
Businesses must also guard against deepfake videos manipulating objects within real footage. Bad actors may be using this to fabricate events or alter visual evidence.
To detect them:
- Observe physics and movement: Pay attention to how objects move in the video. Does their motion appear natural and consistent with the laws of physics? Look for unnatural movement patterns as well as sudden changes in object size, or inconsistencies in lighting and shadows.
- Seek original footage: If possible, try to find the original source of the video footage. This can help you compare it to the manipulated version and identify alterations.

Staying vigilant and applying critical thinking are crucial in the age of deepfakes.
Employees must be equipped with a comprehensive understanding of the diverse forms that deepfakes can take. This entails discerning subtle discrepancies or anomalies that might signal a fabricated video or audio clip. Moreover, deepfake detection requires a commitment to verifying information through reputable channels or sources before accepting it as authentic.
By fostering a proactive stance toward deepfake detection and mitigation, businesses can bolster their resilience against potential threats. Employees serve as the initial line of defense, armed with the knowledge and skills to identify and address deepfake-related risks.
Regular training sessions and educational initiatives can further empower staff members to navigate the evolving landscape of digital deception. By instilling a collective sense of responsibility and preparedness, organizations can effectively fortify their defenses and safeguard their integrity in the face of deepfake challenges.
Is your business ready?
- Do you have a thorough understanding of your fraud detection process?
- Do you have a thorough understanding of the current threat landscape, including deepfakes and deepfake detection?
- Have you assessed the legal ramifications of deepfakes for your organization and devised strategies to minimize risks?
- Is your IT infrastructure security equipped to counter deepfake threats effectively?