Our strategic solutions will keep you on the cutting edge of your industry.
Our Managed Services
Cybersecurity
Risk Assessment
Understand your organization's vulnerability to cyber threats.
Penetration
Testing
Identify security weaknesses through controlled simulations
Managed Detection
& Response (MDR)
Continuous network monitoring for threats and swift responses to security incidents
Secure
Email
Safeguard your email communication from phishing, malware, and other cyber threats
Disaster
Recovery
Ensure business continuity by creating a robust plan to recover from data loss or system failures
Cybersecurity
Awareness Training
Educate your employees to recognize and mitigate security risks, strengthening your organization's defenses
Managed SOC
& SIEM Solutions
Elevate your cybersecurity defences by detecting and responding to threats swiftly and efficiently.
Network & Infrastructure Management
Streamline your network and infrastructure for optimal performance and security.
Help Desk & Remote IT Support
Get immediate 24/7 technical assistance and support from experts, regardless of your location.
Vendor Management
Effortlessly manage and optimize your relationships with technology vendors.
IT Staffing Solutions
Source skilled IT professionals with our dedicated IT staffing solutions in Toronto and the GTA.
IT Consulting
Gain strategic insights and guidance to maximize your IT investments.
Voice Solutions
Revolutionize your business communication with advanced voice solutions tailored to your needs.
Asset Planning & Procurement
We strategically plan and procure software and hardware for cost-effective and efficient operations.
IT Audits & Assessments
Embrace innovative technologies to revamp and future-proof your business
Office IT Relocation
Trust our expertise to handle the intricate process of moving your entire office IT environment, including infrastructure, cabling, and hardware.
Managed Services for New Businesses
With our expertise in IT infrastructure deployment, consulting, cybersecurity, and network solutions, we alleviate the burden of managing your technological needs, allowing you to focus on core business operations and innovation.
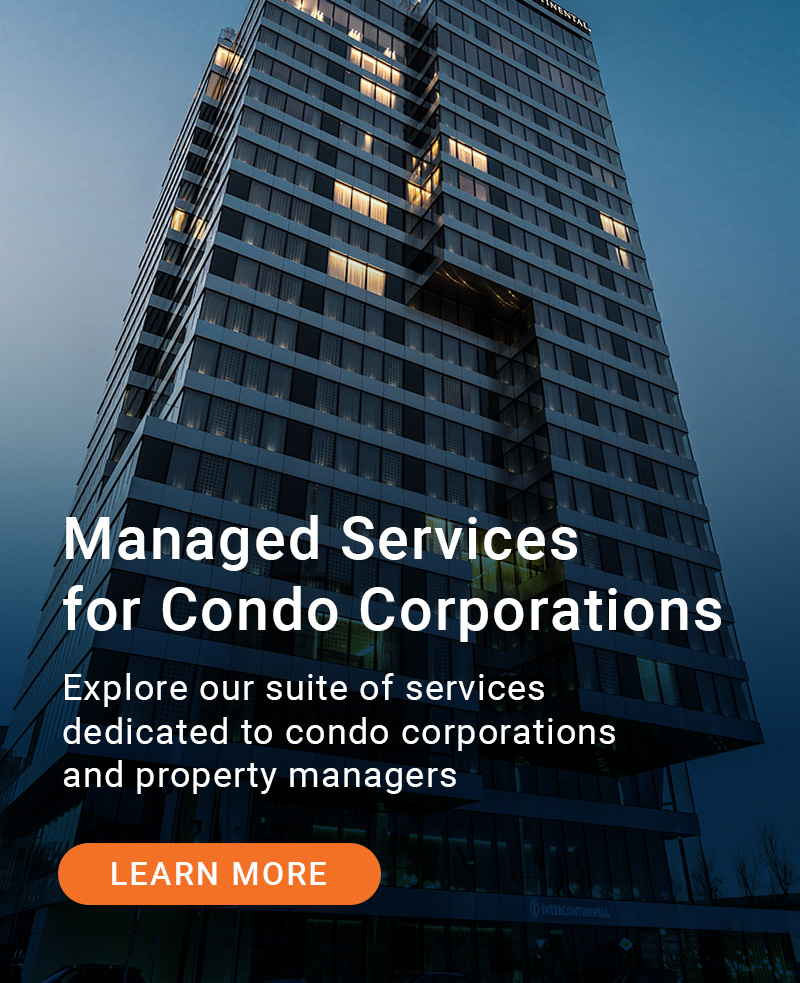
Managed Services for Condominium Corporations
Explore our comprehensive suite of managed services dedicated to condominium corporations and property managers.
Cloud Audits
& Assessments
Evaluate your cloud environment to identify vulnerabilities and opportunities for optimization
Cloud Migration
& Integration
Transition to the cloud seamlessly and efficiently
Cloud
Security
Protect your cloud resources, data, and applications
Microsoft 365 Copilot
Is your business ready to embrace the power (and risks) of AI? As a managed service provider, we’re here to guide your business into this new era of enhanced creativity, productivity, and skill development.
AI Deployment
Navigating the complex landscape of artificial intelligence (AI) tools can be overwhelming for many companies. That's why we're here to help you seamlessly integrate AI solutions into your business operations, boosting productivity while ensuring top-notch security measures.
Data Management & Governance
Protect your data assets with secure and effective data governance and management solutions. Businesses today encounter numerous data management, governance, and compliance challenges, driven by the dynamic landscape of technology, regulations, and cybersecurity threats.
Managed IT
Cybersecurity
Cloud






Search Engine People reached out to Synchroworks with inquiries about moving from physical phones to softphones as they shifted to a more hybrid working environment, and reducing their physical footprint at a traditional office space. During discussions, it became evident that the current IT infrastructure no longer matched the organization’s transition to a more flexible work environment.
One of Synchroworks’ professional services clients fell victim to a sophisticated social engineering phishing attack. The client received an authentic-looking email from Microsoft, requesting a password reset. Trusting the email’s legitimacy, the client followed the reset instructions which ultimately led to a compromised account.
Cholkan and Stepczuk LLP are chartered professional accountants operating in the GTA. In 2021, the client required assistance in their office relocation to ensure network security and avoid disruption. This request entailed complete infrastructure installation at the new office as well as a complete hardware move from one office to the other.
When Rosewood Estates Winery first approached Synchroworks, their main objective was to align their digital and on-site sales strategy with the company’s goals and rate of growth. The company operates as an award-winning boutique winery that offers a wide range of products and services to consumers.
Busy Bee Tools (Busy Bee) is a national seller and distributor of tools and manufacturing machines in Canada. In recent years, Busy Bee has seen substantial growth and, as a result, decided to seek out a strategic partner to ensure that their infrastructure can support further growth.
Synchroworks has been asked to deploy secure infrastructure, which comprises of stable internet connectivity, physical and wireless networks, servers, hardware, cyber security, and several healthcare tuned mobile devices to support the surgical team.
A member-owned financial co-operative that offers a wide range of financial products and services to their members approached Synchroworks to assist them with their IT infrastructure, vendor management, cybersecurity, and cloud migration strategies.
Established in 2018, Osteria Gente has quickly garnered a reputation for its delicious food and community of dedicated customers. It is evident that the restaurant’s success and popularity come not only from the dishes it serves, but from the welcoming and authentic environment it creates for everyone who enters its doors.
Over 1000 organizations across Canada trust us to safeguard their business.
We’d love to earn your trust too.
I have been building web sites for 20 years and they are by far the best company I have worked with and they really take care of me and my business. I run a lease transfer market place and they worked very hard in building and designing my vision. They also work extremely hard in servicing my web site and helping me with new ideas. I highly recommend them for any web based product.
OSCAR ORELLANA
AMG Expert & Sales Manager, Mercedes Benz
I have been working with Synchroworks for almost a year now and have had an excellent experience. I have also learned much about emerging technologies as a result of working with Synchroworks as they never hesitate to share their knowledge and find innovative ways to address their client’s needs.
ANNA PALUZZI
Ukrainian Credit Union
Invaluable insights, masterful project management, and top level service. Strongly recommend everyone to work with this incredibly professional group of web, IT, dev, security, consulting, and programming, specialists.
CHUCK KIRKHAM
President, InMarket
Working with Synchroworks over the past year and a half has been an excellent experience. From top to bottom, everyone on their team are true professionals and a pleasure to work with. Getting us migrated from old technology and into the cloud was no easy task, but they really knew their stuff and we were able to fully trust the process with them. We look forward to continuing our partnership with them for the long term.
HANIF BALOLIA
President, Busy Bee Tools
The entire team is helpful and highly skilled. They present several options and path-of-least-resistance ideas to tackle situations as they arise flawlessly. We look forward to working with them in the future.
WILLIAM ROMAN
General Manager, Rosewood
Get Support in
24 Hours or Less
Our IT team operates across Canada and Poland to resolve your technical issues, ensure system stability, and keep your business running smoothly from anywhere. Focus on your core business while we handle your IT needs.